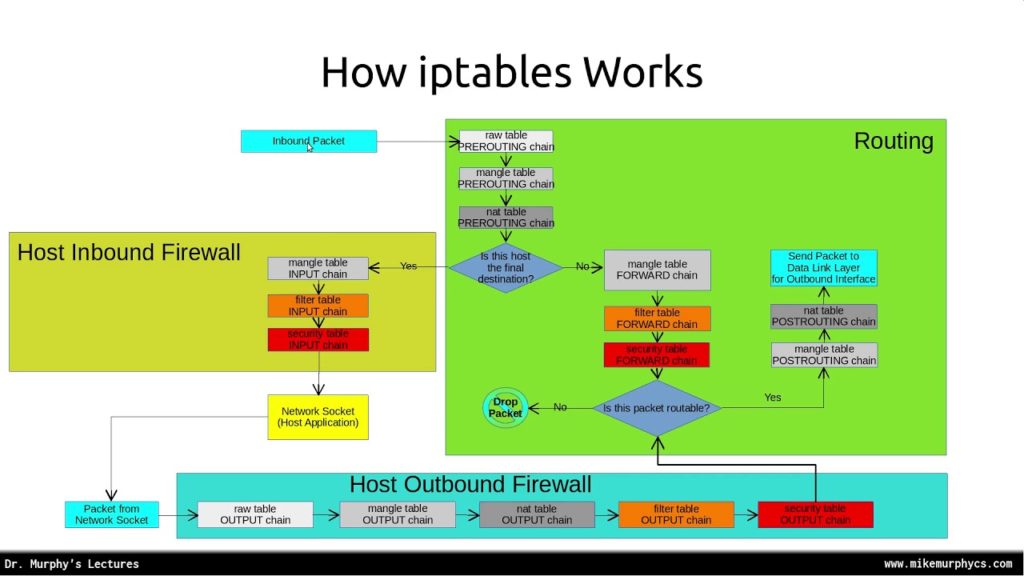
Iptables is one of the most advanced tools for administering networks in Linux. Moreover, this has been used as a firewall since the software allows a system administrator to configure the rules and chains with the tables provided by the Linux kernel system. This post will go through simple use-cases of iptables like how to block an IP address.
Know your tools – An intro to iptables
Iptables is just like any other Linux tool in the plate. It was developed by Rusty Rusell and the Netfilter Core team during the 90s. This utility program is specifically designed to handle IPv4 addresses. However, iptables is just one of the other tools with the -table suffix. It joins its other tools like arptables for ARP and ip6tables for IPv6.

The iptables tool works as root, so take full precaution when using this tool. Also be cautious when granting anyone the privileges to use it.
Using iptables
Iptables has a variety of use-cases. Although for newcomers, learning iptables can prove a bit tricky at first.
For the discerning beginner – using iptables seems like a daunting and lengthy task. But it’s a essential skill anyone needs to pick up when owning a server.
Most of the use-cases boil down to the following:
- Blocking addresses from accessing your server – this is required to prevent brute force attackers trying to brute-force your server’s SSH.
- Packet filtering for your server (wow, that’s some Networking jargon!). Packet filtering allows you to analyze what comes in and out of your server.
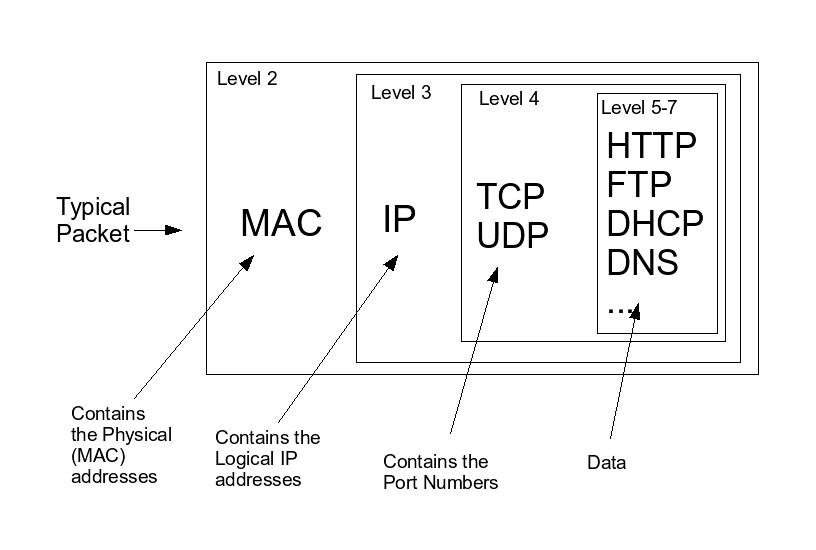
Packets, as defined in networking, are streams of outgoing or incoming data in the network.
Here are a few examples of iptables in action
Blocking an IP address

- Begin by logging as root. (If you’re not signed in as a root user, you’ll need to make sure you have sudo privileges on that user)
- Once confirmed that you have sudo privileges, run this command:
iptables -A INPUT -s IP-ADDRESS -j DROPwhere IP-ADDRESS is the IP address you want to block. - Your server will now bar this IP address when it attempts to connect.
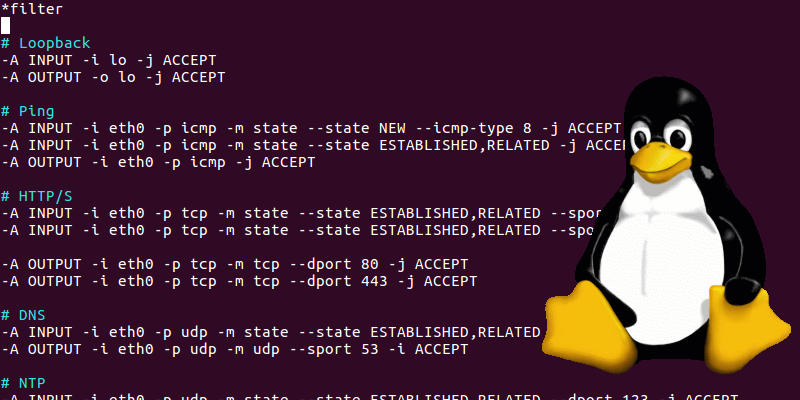
Whitelisting traffic
- Login as root or assure that you have sudo permissions.
- run the following:
iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A INPUT -s 192.168.1.0/24 -j ACCEPT
iptables -P INPUT DROP
iptables -P FORWARD DROP - Your server should now accept requests from the 12.168.1.0/24 CIDR block (whoa, Networking jargon again!).
Iptables works where you least expect it
Some tools in Linux use iptables in the backend. One very striking example of it is fail2ban. Fail2ban uses iptables to temporarily block anyone who will enter the incorrect SSH password on a specific interval.

Another example is firewalld. Firewalld, as its name implies, is a firewall management tool for Linux, and it uses iptables behind the curtains, so you don’t need to.
A beginner’s Iptables guide – Conclusion
Iptables is a powerful tool on its own. While this is configuration-heavy, some power users use it directly to fine-tune their network configuration.
It is not recommended you use iptables if you are inexperienced with Linux networking. It’s important to take time to study how networking works in Linux before you begin to use iptables. However, if you’re ready to dive deeper into some more iptables tutorials, there are some more in-depth guides available online.
Use promo code “SKY95IPTABLES” to save 95% off your first month. Offer is valid for new users only.